Governance That Actually Binds
Sealed telemetry and external enforcement — because policy without runtime control isn’t governance.
The Enforcement Gap No One Wants to Talk About
Most AI governance today is descriptive.
Policies.
Principles.
Alignment layers.
Post-hoc logging.
All of it assumes one thing:
The system will behave — and if it doesn’t, we’ll review it later.
That’s not governance.
That’s documentation.
When systems gain execution authority — the ability to access tools, memory, money, workflows, infrastructure — the risk shifts from narrative to runtime.
The real question becomes:
Who can stop the system at the moment it attempts to act?
If the answer is “we log it” or “we’ll review it” or “we’ll retrain it,”
you don’t have governance.
You have hope.
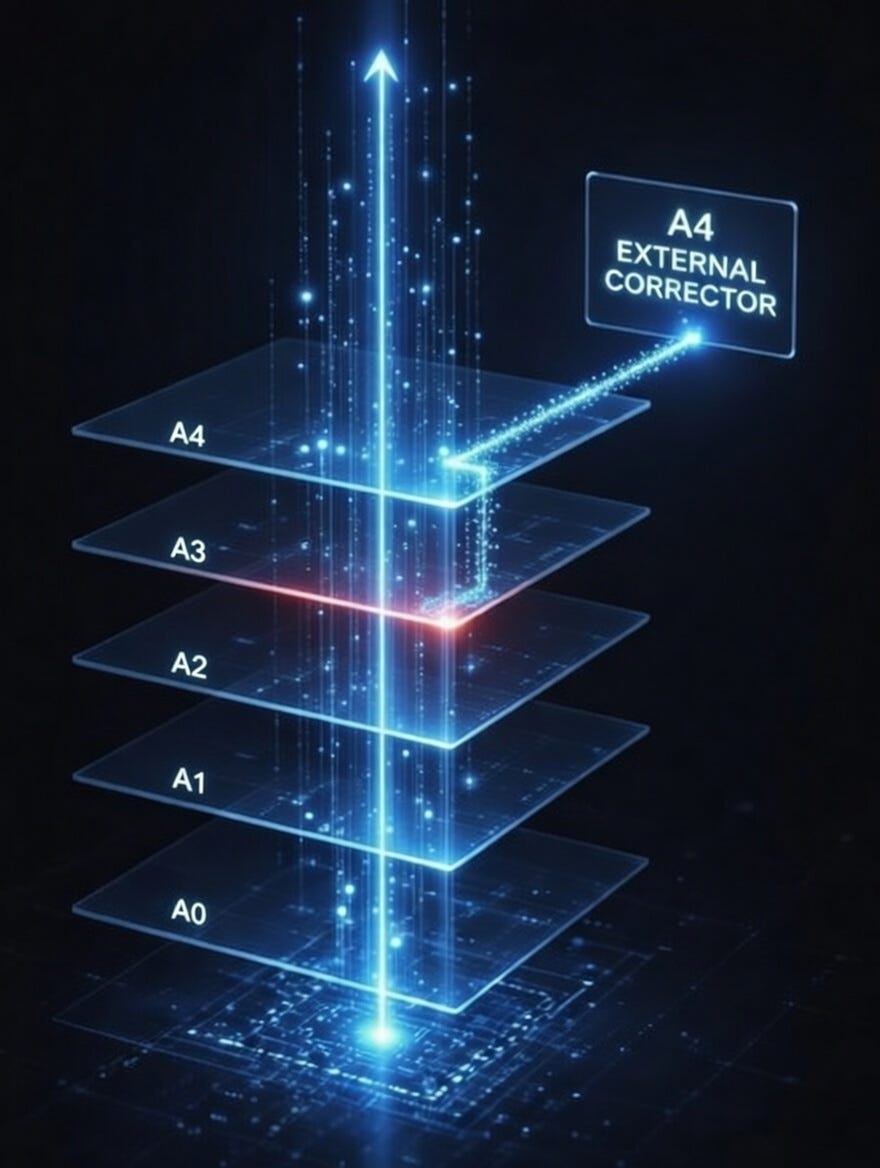
DSS-1 Prevents Drift. DSS-2 Governs Authority.
DSS-1 defined the invariants required to prevent invalid reasoning trajectories from forming.
DSS-2 addresses a different problem:
What happens when a system has runtime authority?
DSS-2 defines minimum structural requirements for:
Layered governance telemetry
Cryptographic sealing of runtime events
Independent validation
Enforceable authority constraints
It governs authority integrity, not model alignment.
That distinction matters.
The Core Shift: From Advice to Impossibility
Most governance frameworks discourage bad behavior.
DSS-2 requires that certain actions be structurally impossible.
If a boundary is crossed:
Execution halts.
If telemetry is tampered with:
Validation fails.
If authority cannot be verified:
Action is refused.
Governance must operate before state change, not after damage.
Why Sealing Matters
If runtime authority events are not sealed:
Logs can be altered.
State transitions can be rewritten.
Validation becomes advisory.
Sealed telemetry means:
Runtime authority events are bound to cryptographic proof.
They can be verified independently.
They cannot be silently rewritten after execution.
Without sealing, enforcement is cosmetic.
Why External Validation Matters
If a system validates its own authority,
it is marking its own homework.
DSS-2 requires independent validation in a separate trust domain.
That means:
The actor and the validator are not the same.
Authority is confirmed externally.
Enforcement does not rely on self-reporting.
Without separation, governance collapses into self-permission.
Certification Claims Must Bind
Claiming conformance to governance standards should not be a marketing statement.
DSS-2 requires that certification claims include:
Active enforcement gates
Observable runtime telemetry
Verifiable validation pathways
If enforcement is advisory, the claim is void.
Governance must bind at runtime.
What DSS-2 Is Not
It is not:
A new alignment philosophy
A prompt strategy
A compliance checklist
A logging recommendation
It is a structural standard for execution authority integrity.
It assumes:
If a system can act,
that act must be admissible —
and admissibility must be enforceable.
The Larger Context
As systems become agentic:
They access external tools.
They manage workflows.
They influence financial and operational outcomes.
They operate with increasing autonomy.
The governance conversation cannot stay at the narrative layer.
It must move to the authority layer.
DSS-2 formalizes that shift.
Final Principle
Governance that cannot halt execution is not governance.
It is commentary.
DSS-1 defined the invariants required to prevent invalid reasoning trajectories from forming.
DSS-2 defines the minimum structural requirements for governance that binds.